# Security Through Transparency
## dApps on IPFS
Anybody who watches [The Lock Picking Lawyer](https://www.youtube.com/c/lockpickinglawyer) knows that traditional security is provided mostly through obscurity, as he demonstrates with nearly every video that this kind of "security" is no security at all.
I've just put the last checks together that I believe makes the dlux dApp distribution scheme as secure as any traditional website. Let's talk about how this works, pose a challenge, and invite some commentary.
## Arbitrary Code Execution
The real name of the game is executing arbitrary code in a certain context. Traditional websites have had this exploit thru all sorts of means and if you decide to build a dApp on DLUX you'll have the same expectations of knowledge as any normal website developer. Things that we can't control are obviously out of bounds, such as setting up a phishing website and getting a user to click a link in an email. However, the way dlux dApps are set up it was possible to to send somebody a link, get them to load a page inside of the same sandbox as usual... which would mean exposing that dApps data through cookies, localStorage, and even sessionStorage in some cases. Depending on the nature of the dApp this could mean leaking valuable information.
## DLUX dApp Paradigm
In a few words DLUX dApps should be roughly identical to setting up your own static website, on your own server, with your own SSL certificates. There are numerous ways to accomplish the same thing on today's internet such as github pages. The major differences here are instead of free hosting, Hive has content rewards. Posting an app on github pages like [The SPK Network Monitor](https://hiveuprss.github.io/spkccmonitor/) won't earn you any cryptocurrency and has the possibility of being censored or deleted by Github.
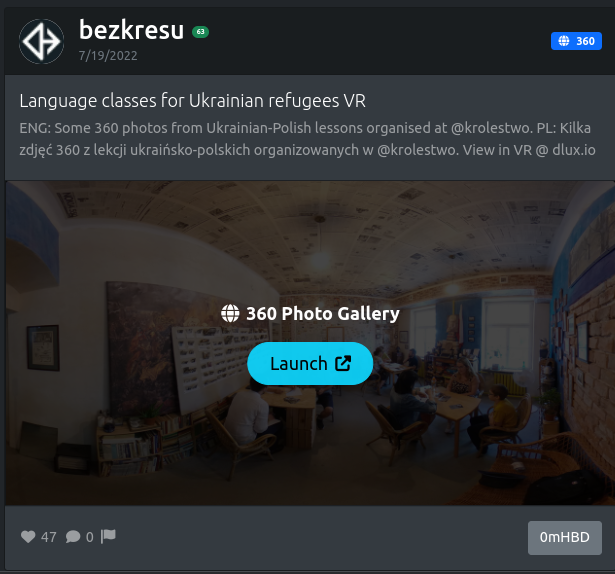
[DLUX | Language classes for Ukrainian refugees in VR](https://bezkresu.ipfs.dlux.io/?undefined&hash=QmNby3SMAAa9hBVHvdkKvvTqs7ssK4nYa2jBdZkxqmRc16&author=bezkresu&permlink=language-classes-for-ukrainian-refugees-vr) is a very simple dApp that just displays some 360 images. If I wanted to censor this dApp I could, but the goal of decentralization is to have multiple people run multiple frontends, or even have a local application that can deliver this content no matter the whims of certain individuals.
I hope this paradigm meets or exceeds any other UX for both the developer and the user in terms of speed, trust, security, and usability.
### Breaking Down DLUX Security
Using the above dApp; looking at the domain you will find bezkresu.ipfs.dlux.io. It's set up in such a way that only @bezkresu can post dApps that will run from this domain. Let's find out how this works.
Clicking on this app from dlux.io will generate this link:
https://www.dlux.io/dlux/@bezkresu/language-classes-for-ukrainian-refugees-vr
#### Links to dlux.io
This link will likely benefit from a HEAD request to enable link previews. GET requests will have dlux.io will serve this static [file](https://github.com/dluxio/dlux-iov/blob/main/dlux/index.html) with the following interesting code.
```js
const author = window.location.pathname.split('/')[2].replace('@', '')
const permlink = window.location.pathname.split('/')[3]
fetch("https://api.hive.blog")
.then((r) => r.json())
.then(res => {
stateObj = res.result
metadata = stateObj.json_metadata
hashy = JSON.parse(metadata).vrHash,
vars = `?${location.href.split('?')[1]}` || `?`
//...
function match (s,t) {var a=[];for(var i=0;i<s.length;i++){j=s.indexOf(t,i);if(j>=0){a.push(j);i=j}else return a}}
subauthor = match(author,'.').length ? match(author,'.').join('') + author.replace('.', '-') : author
ipfsdomain = `https://${subauthor}.ipfs.dlux.io`;
location.href = ipfsdomain + `${vars}&hash=${hashy}&author=${author}&permlink=${permlink}&user=${user}`
```
It forwards the request to an IPFS enabled subdomain. Probably the hardest thing to understand here is Hive Accounts can have a . in them which would make this subdomain 2 or more subdomains. If @your.app account created a dApp, @your-app could be made to post a dApp that could access @your.app's subdomain. Since hive accounts can't start with a number, this will be used as a place to index where .'s are replaced with -'s. your-app and 4your-app in this case.
#### Managing an iFrame
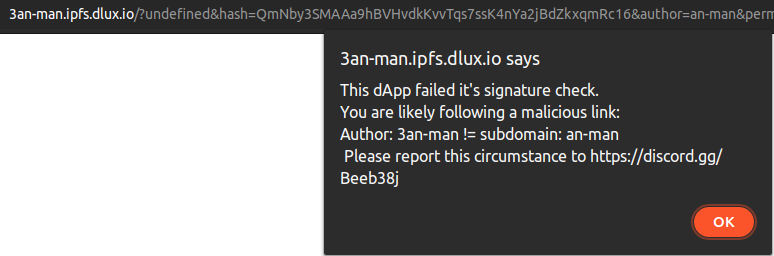
Our IPFS server only has one file to serve. This file checks some signatures indirectly and puts the dApp in an iFrame. Let's see how this works.
```
dns01 = window.location.hostname.split('.')[0]
dots = match(author,'.')
authorizedDNS01 = dots.length ? dots.join('') + author.replaceAll('.', '-') : author
if(dns01 != authorizedDNS01){
goAhead = false
alert(`This dApp failed it's signature check.\nYou are likely following a malicious link:\nAuthor: ${dns01}
!= subdomain: ${authorizedDNS01}\n Please report')
}
```
The match function is the same as above. It does it's own check to see if it's on an authorized subdomain before asking a Hive API for the post content. The user following a link to an unqualified domain will get a warning message and no iFrame will be set up.
#### Caddy Configuration
Finally, to serve anything out of our IPFS's subdomain gateway we've configured [Caddy](https://caddyserver.com/) as follows.
```
*.ipfs.dlux.io {
root * /var/www/html/ipfs
file_server
@ipfs {
header Referer https://{labels.3}.ipfs.dlux.io*
}
handle @ipfs {
reverse_proxy /ipfs/* localhost:8080
}
tls {
dns cloudflare {api-key}
}
}
```
`*.ipfs.dlux.io` handles our wildcard subdomain.
`file_server` serves our one and only file that checks subdomains, and set's up the iFrame sandbox
`@ipfs` defines a rule where the referer matches the current subdomain
`handle @ipfs` forwards ipfs/CIDs to the IPFS instance to load out the dApp.
`tls` give Caddy the information it needs to keep our SSL certs up to date.
### Capture the Flag
I've put a 'secret' in my localStorage.
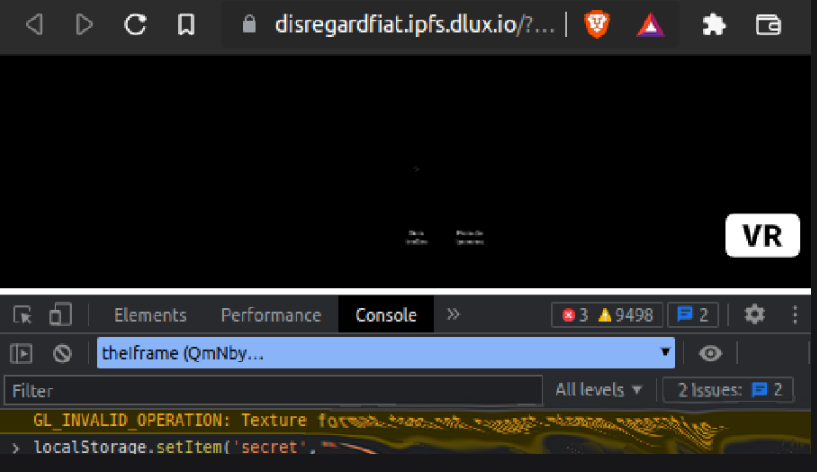
It's sha256 hash is as follows: `16f20aed9b0f3a773f890c54936ed60df1c9d225723e2b9b7c89f30cd1bb3146`
I'll click on any link posted below. If you can get my secret from my localStorage I'd love to know how. So much in fact that I'll offer a 50,000 DLUX bounty (or 500 Hive).
If you can think of improvements, I want to know. If you have questions, ask them.
I hope that our sandbox is just as secure as any other website. That phishing out of a non-managed url is the best an attacker can do... and the sandbox only executes code that the author wrote.
As always, a vote for my witness or approval of [proposal 234](https://peakd.com/proposals/234) helps me out.| author | disregardfiat |
|---|---|
| permlink | dlux-dapp-security-deep-dive |
| category | hive |
| json_metadata | "{"app":"peakd/2022.10.3","format":"markdown","description":"Wth a Capture the Flag challenge.","tags":["hive","dlux","ipfs","dev","security","dapp","defi"],"users":["bezkresu","your.app","your-app","ipfs"],"image":["https://files.peakd.com/file/peakd-hive/disregardfiat/23tRvMrX4xVmZiU9GsgYQ1eAYKjrwvbJEiQiFPUy1kNp7wJUtuzNnA2FrVpMy1uTFvzDM.png","https://files.peakd.com/file/peakd-hive/disregardfiat/Eqqvm2VzyWEKjUMEnZ74DwqA1QGce6Z4LbmZy8UDEq67VsRnUuKQ3GvCKeCpLmBbo5f.png","https://files.peakd.com/file/peakd-hive/disregardfiat/23wfmxBxLZG7V7B5EUWySMZugC6w5xj2PvwtsDhjfZ2jnPpAdv1vB7sn3tap2fbDZteqm.png"]}" |
| created | 2022-10-27 05:02:36 |
| last_update | 2022-10-27 05:02:36 |
| depth | 0 |
| children | 7 |
| last_payout | 2022-11-03 05:02:36 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 62.806 HBD |
| curator_payout_value | 62.727 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 7,197 |
| author_reputation | 348,256,954,150,586 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,817,663 |
| net_rshares | 202,902,558,593,701 |
| author_curate_reward | "" |
| voter | weight | wgt% | rshares | pct | time |
|---|---|---|---|---|---|
| kencode | 0 | 1,417,279,015,157 | 100% | ||
| flemingfarm | 0 | 278,947,332,114 | 50% | ||
| acidyo | 0 | 6,264,319,804,794 | 50% | ||
| ausbitbank | 0 | 1,784,402,667,108 | 100% | ||
| ardina | 0 | 16,625,542,870 | 100% | ||
| jeffjagoe | 0 | 982,109,822 | 0.08% | ||
| kendewitt | 0 | 265,833,665,002 | 100% | ||
| fiona777 | 0 | 1,870,458,095 | 50% | ||
| jphamer1 | 0 | 2,935,728,906,888 | 100% | ||
| randomblock1 | 0 | 1,910,945,030 | 25% | ||
| anarcist69 | 0 | 3,660,269,171 | 2.1% | ||
| alchemage | 0 | 9,607,847,025 | 10% | ||
| theb0red1 | 0 | 64,536,766,225 | 20% | ||
| elamental | 0 | 1,280,346,846 | 2.77% | ||
| stevescoins | 0 | 723,618,388 | 7.5% | ||
| netaterra | 0 | 365,180,490,902 | 15% | ||
| penguinpablo | 0 | 263,656,735,369 | 14% | ||
| wakeupnd | 0 | 99,731,764,346 | 50% | ||
| jimbobbill | 0 | 2,209,659,049 | 15% | ||
| titusfrost | 0 | 31,312,994,988 | 100% | ||
| appalachain | 0 | 1,065,946,592 | 2.1% | ||
| funnyman | 0 | 1,349,793,555 | 5.6% | ||
| disregardfiat | 0 | 362,610,451,334 | 100% | ||
| ssekulji | 0 | 35,422,361,102 | 100% | ||
| ura-soul | 0 | 13,177,529,788 | 7.5% | ||
| edb | 0 | 23,394,195,788 | 20% | ||
| mow | 0 | 1,326,495,584 | 100% | ||
| v4vapid | 0 | 1,586,139,791,216 | 9.9% | ||
| teammo | 0 | 146,996,323,012 | 100% | ||
| ranchorelaxo | 0 | 42,505,676,706,686 | 100% | ||
| diggndeeper.com | 0 | 5,668,367,993,838 | 100% | ||
| louisthomas | 0 | 107,839,704,512 | 100% | ||
| freebornsociety | 0 | 10,540,309,244 | 7% | ||
| detlev | 0 | 58,426,217,294 | 5% | ||
| passion-fruit | 0 | 8,876,532,913 | 100% | ||
| fortune-master | 0 | 8,452,996,561 | 100% | ||
| mes | 0 | 510,316,218,564 | 100% | ||
| amberyooper | 0 | 7,206,028,115 | 20% | ||
| newsflash | 0 | 1,239,076,875,732 | 2.47% | ||
| jonsnow1983 | 0 | 14,786,587,686 | 100% | ||
| alphacore | 0 | 3,119,855,692 | 2.82% | ||
| tracer-paulo | 0 | 21,300,647,116 | 100% | ||
| firstamendment | 0 | 125,366,022,252 | 100% | ||
| hellene8 | 0 | 876,067,728 | 40% | ||
| truthforce | 0 | 914,974,739 | 15% | ||
| joeyarnoldvn | 0 | 598,887,883 | 1.76% | ||
| theouterlight | 0 | 148,196,646,917 | 100% | ||
| bluemist | 0 | 21,482,874,530 | 10% | ||
| lenasveganliving | 0 | 2,424,737,715 | 5% | ||
| drorion | 0 | 762,761,430,968 | 95% | ||
| haejin | 0 | 10,552,167,308,489 | 100% | ||
| appreciator | 0 | 38,113,546,835,542 | 10% | ||
| isabelpena | 0 | 15,828,597,911 | 100% | ||
| pocketrocket | 0 | 14,792,943,934 | 100% | ||
| steemik | 0 | 642,995,862,190 | 100% | ||
| muxxybot | 0 | 7,310,709,556 | 50% | ||
| amitsharma | 0 | 121,120,065,506 | 100% | ||
| ernick | 0 | 16,969,439,401 | 100% | ||
| jonyoudyer | 0 | 8,092,329,596 | 10% | ||
| aafeng | 0 | 8,230,428,238 | 1% | ||
| evernoticethat | 0 | 11,428,601,424 | 100% | ||
| crrdlx | 0 | 63,325,494,056 | 100% | ||
| santigs | 0 | 32,051,788,503 | 50% | ||
| floatinglin | 0 | 5,254,733,641 | 100% | ||
| tonygreene113 | 0 | 1,507,069,394 | 10% | ||
| chinchilla | 0 | 282,265,976,218 | 100% | ||
| karlin | 0 | 78,192,299,998 | 100% | ||
| revisesociology | 0 | 2,254,598,715,230 | 100% | ||
| oizaguirres | 0 | 11,905,014,746 | 100% | ||
| risemultiversity | 0 | 1,047,670,199 | 7.5% | ||
| jamiekensell | 0 | 704,739,953 | 80% | ||
| the-imposter | 0 | 603,989,755 | 64% | ||
| happydolphin | 0 | 25,356,965,587 | 17% | ||
| jordan.lesich | 0 | 8,189,086,819 | 100% | ||
| xuanphuc98 | 0 | 5,088,000,117 | 100% | ||
| x30 | 0 | 141,561,372,354 | 10% | ||
| arabisouri | 0 | 101,145,340,715 | 100% | ||
| noble-noah | 0 | 18,737,349,501 | 100% | ||
| informationwar | 0 | 93,024,570,265 | 15% | ||
| socent | 0 | 1,506,719,887 | 15% | ||
| mightpossibly | 0 | 357,311,554,029 | 100% | ||
| shadow3scalpel | 0 | 41,542,774,615 | 80% | ||
| sunsea | 0 | 6,415,860,579 | 5% | ||
| paulmoon410 | 0 | 1,267,512,925 | 10% | ||
| irynochka | 0 | 3,365,680,225 | 100% | ||
| hispeedimagins | 0 | 19,710,144,106 | 50% | ||
| thewritersblock | 0 | 5,133,465,531 | 100% | ||
| hojaraskita | 0 | 1,383,666,981 | 100% | ||
| leninbracho50 | 0 | 158,665,009,313 | 100% | ||
| elderson | 0 | 1,228,152,181 | 2.1% | ||
| fjcalduch | 0 | 184,183,469,665 | 50% | ||
| petronila | 0 | 751,008,971 | 100% | ||
| dmwh | 0 | 19,639,834,560 | 7.5% | ||
| cryptonized | 0 | 21,717,424,809 | 14% | ||
| rodyservi | 0 | 1,007,386,471 | 100% | ||
| gibber | 0 | 1,960,899,518 | 32% | ||
| pexpresiones | 0 | 39,003,540,347 | 100% | ||
| hallmann | 0 | 563,250,967,657 | 100% | ||
| iamevilradio | 0 | 8,375,048,077 | 40% | ||
| empress-eremmy | 0 | 18,223,048,299 | 7.5% | ||
| yolmare | 0 | 51,706,276,390 | 100% | ||
| ikrahch | 0 | 195,605,809,883 | 50% | ||
| fundacja | 0 | 67,494,930,805 | 100% | ||
| nacarid | 0 | 563,657,550 | 100% | ||
| ninachejov | 0 | 1,778,836,293 | 100% | ||
| shmoogleosukami | 0 | 30,113,887,766 | 100% | ||
| eddiespino | 0 | 2,744,719,664,091 | 100% | ||
| jadams2k18 | 0 | 1,000,232,182 | 100% | ||
| lisfabian | 0 | 19,963,548,572 | 50% | ||
| jagoe | 0 | 71,063,607,690 | 24% | ||
| ange.nkuru | 0 | 433,830,707 | 3% | ||
| tonytrillions | 0 | 1,891,926,231 | 60% | ||
| madpotters | 0 | 1,331,889,145 | 30% | ||
| outlinez | 0 | 2,158,300,296 | 5% | ||
| manniman | 0 | 653,948,906,303 | 100% | ||
| karolines | 0 | 6,021,938,484 | 100% | ||
| reversehitler88 | 0 | 13,573,173,601 | 100% | ||
| franciscopr | 0 | 16,151,997,481 | 100% | ||
| racibo | 0 | 12,285,494,255 | 50% | ||
| m2nnari | 0 | 6,719,330,388 | 100% | ||
| axeltheartist | 0 | 6,808,455,886 | 100% | ||
| inciter | 0 | 6,299,490,553 | 10% | ||
| cyemela | 0 | 50,400,946,051 | 100% | ||
| tsnaks | 0 | 8,915,534,753 | 100% | ||
| reinmar | 0 | 1,025,321,460 | 100% | ||
| kgakakillerg | 0 | 17,302,649,541 | 10% | ||
| meanbees | 0 | 545,355,523 | 0.42% | ||
| veteranforcrypto | 0 | 9,523,100,920 | 40% | ||
| dlux-io | 0 | 1,723,026,757,076 | 100% | ||
| fw206 | 0 | 4,014,145,277,183 | 100% | ||
| davidesimoncini | 0 | 10,316,686,950 | 27.9% | ||
| steem-tube | 0 | 6,959,436,075 | 100% | ||
| motherofalegend | 0 | 588,828,155 | 2.1% | ||
| realkiki85 | 0 | 4,807,311,236 | 100% | ||
| commonlaw | 0 | 4,914,390,603 | 35% | ||
| ua-promoter | 0 | 5,266,430,801,487 | 100% | ||
| marblely | 0 | 9,660,768,876 | 10% | ||
| haccolong | 0 | 27,567,037,753 | 70% | ||
| alcidescadiz | 0 | 62,460,991,063 | 100% | ||
| pignys | 0 | 36,298,755,325 | 100% | ||
| ambiguity | 0 | 7,745,557,945 | 20% | ||
| skryptorium | 0 | 575,911,671 | 100% | ||
| cyrusemerson | 0 | 130,240,160,581 | 100% | ||
| hoaithu | 0 | 14,922,583,201 | 59.5% | ||
| aconsciousness | 0 | 2,270,000,174 | 95% | ||
| deepdives | 0 | 122,927,514,745 | 15% | ||
| bezkresu | 0 | 8,291,426,484 | 100% | ||
| junior182 | 0 | 821,250,938 | 100% | ||
| anhvu | 0 | 11,105,577,713 | 56% | ||
| bengiles | 0 | 8,153,561,474 | 1.05% | ||
| reteem | 0 | 2,353,464,111 | 70% | ||
| canna-curate | 0 | 26,173,202,663 | 4.2% | ||
| darkprince66 | 0 | 537,410,670 | 100% | ||
| piensocrates | 0 | 8,592,500,872 | 100% | ||
| courtneyjensen | 0 | 3,568,488,764 | 100% | ||
| mister-meeseeks | 0 | 22,838,775,924 | 25% | ||
| athunderstruck | 0 | 871,062,534 | 2.1% | ||
| balticbadger | 0 | 1,758,602,913 | 20% | ||
| riskneutral | 0 | 1,713,038,546 | 15% | ||
| krolestwo | 0 | 10,538,594,727 | 100% | ||
| brianoflondon | 0 | 3,147,066,729,192 | 100% | ||
| douglasjames | 0 | 16,712,883,034 | 100% | ||
| marinmex | 0 | 5,947,036,836 | 100% | ||
| celi130 | 0 | 283,754,042,321 | 100% | ||
| theycallmedan | 0 | 51,836,776,732,675 | 60% | ||
| chisdealhd | 0 | 7,036,248,124 | 30% | ||
| redheaddemon | 0 | 888,690,537 | 40% | ||
| bluerobo | 0 | 137,797,635,715 | 100% | ||
| dfen | 0 | 1,854,874,229 | 100% | ||
| jacuzzi | 0 | 2,269,377,872 | 1.4% | ||
| apokruphos | 0 | 3,304,265,429 | 1% | ||
| steemitmonsters | 0 | 1,047,432,939 | 100% | ||
| hungrybear | 0 | 606,660,734 | 14% | ||
| thelogicaldude | 0 | 59,167,622,181 | 50% | ||
| janyasai | 0 | 8,773,012,293 | 30% | ||
| denizcakmak | 0 | 1,047,289,579 | 100% | ||
| kharma.scribbles | 0 | 1,345,856,324 | 75% | ||
| marymi | 0 | 3,802,806,444 | 100% | ||
| russia-btc | 0 | 804,455,449,549 | 45% | ||
| guysellars | 0 | 1,347,040,167 | 100% | ||
| ruggedbeardmedia | 0 | 509,842,396 | 100% | ||
| maxsieg | 0 | 2,230,429,672 | 15% | ||
| chunkysoupsvc | 0 | 36,182,490,593 | 100% | ||
| steemadventures | 0 | 499,743,620 | 80% | ||
| bonfirepit | 0 | 498,988,422 | 100% | ||
| concreteshallows | 0 | 497,217,967 | 100% | ||
| photographercr | 0 | 22,233,037,916 | 10% | ||
| frugalgamer | 0 | 1,149,647,245 | 100% | ||
| yiobri | 0 | 9,968,952,474 | 100% | ||
| javiersebastian | 0 | 19,703,085,750 | 100% | ||
| coolsurfer | 0 | 1,067,966,011 | 5% | ||
| beerlover | 0 | 6,637,655,815 | 5% | ||
| kresykresow | 0 | 1,440,213,818 | 100% | ||
| clownworld | 0 | 652,371,746 | 7.5% | ||
| iktisat | 0 | 653,689,050 | 100% | ||
| anosys | 0 | 1,280,854,955 | 50% | ||
| trichomesnetwork | 0 | 1,107,604,999 | 100% | ||
| freedomring | 0 | 15,260,474,509 | 80% | ||
| thranax | 0 | 8,514,986,926 | 25% | ||
| urun | 0 | 62,679,995,201 | 100% | ||
| shtup | 0 | 319,937,345,987 | 100% | ||
| electronico | 0 | 1,632,597,876 | 100% | ||
| oratione | 0 | 861,182,300 | 100% | ||
| zeesh | 0 | 2,434,879,406 | 5% | ||
| therealyme | 0 | 4,382,900,769 | 15% | ||
| blocktvnews | 0 | 884,031,988 | 50% | ||
| atma.love | 0 | 14,650,016,615 | 3% | ||
| marblesz | 0 | 657,256,358 | 10% | ||
| softworld | 0 | 226,101,031,211 | 48% | ||
| nildasalazar | 0 | 1,421,864,220 | 100% | ||
| ninnu | 0 | 24,227,739,227 | 25% | ||
| invest4free | 0 | 6,766,196,241 | 40% | ||
| ghaazi | 0 | 2,735,067,705 | 50% | ||
| actioncats | 0 | 14,973,875,412 | 10% | ||
| discoveringarni | 0 | 43,183,028,602 | 15% | ||
| noelyss | 0 | 2,923,941,081 | 5% | ||
| balvinder294 | 0 | 12,553,488,866 | 100% | ||
| lucianav | 0 | 1,365,071,098 | 5% | ||
| hivebuildercomps | 0 | 2,312,573,887 | 100% | ||
| zhoten | 0 | 16,530,726,449 | 50% | ||
| obandoduarte | 0 | 19,571,625,635 | 100% | ||
| reward.app | 0 | 346,610,397,757 | 50% | ||
| portsundries | 0 | 1,839,551,711 | 100% | ||
| sevalo13 | 0 | 2,303,396,818 | 100% | ||
| josemoises | 0 | 3,748,159,570 | 100% | ||
| sevenoh-fiveoh | 0 | 5,663,273,029 | 25% | ||
| cccoinx.voter | 0 | 818,746,723 | 50% | ||
| yosmandiaz | 0 | 548,296,020 | 100% | ||
| hermaryrc | 0 | 6,222,983,095 | 100% | ||
| noalys | 0 | 663,957,103 | 5% | ||
| kattycrochet | 0 | 4,138,413,963 | 5% | ||
| chubb149 | 0 | 1,200,131,691 | 6% | ||
| n0m0refak3n3ws | 0 | 1,793,824,055 | 7.5% | ||
| cocaaladioxine | 0 | 1,544,386,258 | 100% | ||
| specific | 0 | 374,893,110,005 | 100% | ||
| libertytokens27 | 0 | 644,070,483 | 100% | ||
| cielitorojo | 0 | 8,694,671,430 | 7% | ||
| sofs-su | 0 | 85,415,798,808 | 68.2% | ||
| therealsnowjon | 0 | 11,354,467,788 | 80% | ||
| firinmahlazer | 0 | 508,261,982 | 100% | ||
| nj07 | 0 | 3,890,035,341 | 100% | ||
| elgatoshawua | 0 | 2,121,688,716 | 5% | ||
| melcaya | 0 | 38,775,099,143 | 100% | ||
| drricksanchez | 0 | 35,791,470,469 | 7.5% | ||
| hykss.nature | 0 | 1,263,531,626 | 100% | ||
| rendrianarma | 0 | 1,049,380,613 | 25% | ||
| hexagono6 | 0 | 1,143,099,887 | 5% | ||
| todkrank | 0 | 6,432,575,301 | 100% | ||
| leveluplifestyle | 0 | 11,626,779,774 | 25% | ||
| robertmendontza | 0 | 1,741,038,885 | 100% | ||
| ksiazki | 0 | 3,155,184,312 | 100% | ||
| power-kappe | 0 | 687,582,730 | 10% | ||
| hive.friends | 0 | 0 | 1% | ||
| primalamusica | 0 | 265,721,815,780 | 50% | ||
| shanhenry | 0 | 2,446,219,623 | 100% | ||
| fotomaglys | 0 | 1,680,658,538 | 5% | ||
| lordb | 0 | 2,732,215,819 | 100% | ||
| hivehydra | 0 | 1,599,643,431 | 90% | ||
| readthisplease | 0 | 1,056,795,149 | 1.6% | ||
| podping | 0 | 399,408,892,464 | 100% | ||
| lpa | 0 | 5,281,959,980 | 100% | ||
| jaybone | 0 | 2,092,353,245 | 100% | ||
| rimurutempest | 0 | 4,478,488,563 | 100% | ||
| irenicus30 | 0 | 29,924,152,688 | 100% | ||
| aprasad2325 | 0 | 1,891,610,070 | 5% | ||
| delver | 0 | 6,086,661,796 | 15% | ||
| pishio | 0 | 556,007,325,043 | 10% | ||
| jongcl | 0 | 2,473,088,801 | 9% | ||
| cryptoccshow | 0 | 5,988,185,598 | 50% | ||
| esteva1820 | 0 | 683,159,760 | 100% | ||
| quycmf8 | 0 | 168,916,589,055 | 10% | ||
| onwugbenuvictor | 0 | 6,676,474,330 | 15% | ||
| epsilon27 | 0 | 48,835,667,379 | 100% | ||
| xclie | 0 | 0 | 100% | ||
| cyboule | 0 | 28,211,016,738 | 100% | ||
| waffleuncle | 0 | 2,290,043,301 | 30% | ||
| trasto | 0 | 2,315,767,005 | 25% | ||
| wendy0520 | 0 | 483,764,499 | 9% | ||
| pay2earn | 0 | 1,959,790,098 | 50% | ||
| dsky | 0 | 915,078,642,848 | 100% | ||
| jordand89 | 0 | 52,091,200,272 | 100% | ||
| deraaa | 0 | 2,699,555,026 | 10% | ||
| nawalz | 0 | 1,841,554,260 | 100% | ||
| mengao | 0 | 95,403,843,298 | 100% | ||
| estherscott | 0 | 658,551,033 | 4% | ||
| uncorked-reality | 0 | 1,874,781,656 | 50% | ||
| violator101 | 0 | 26,023,852,951 | 100% | ||
| winniecorp | 0 | 793,202,483 | 8% | ||
| drexlord | 0 | 3,653,209,181 | 7.5% | ||
| aichanbot | 0 | 18,096,655,703 | 50% | ||
| svanbo | 0 | 835,739,915 | 10% | ||
| omosefe | 0 | 594,437,454 | 8% | ||
| saboin.weed | 0 | 1,093,634,033 | 11.7% | ||
| imoogin3v3rm0r3 | 0 | 3,109,910,974 | 30% | ||
| sagarkothari88 | 0 | 42,613,868,695 | 5% | ||
| femcy-willcy | 0 | 590,197,798 | 5% | ||
| zerofucks | 0 | 4,597,996,143 | 100% | ||
| hironakamura | 0 | 2,960,687,496 | 16% | ||
| bosveld1 | 0 | 1,076,566,153 | 100% | ||
| martinlazizi | 0 | 540,346,418 | 16% | ||
| lukasbachofner | 0 | 775,848,228 | 3% | ||
| wannatrailwithme | 0 | 1,744,378,613 | 50% | ||
| investinfreedom | 0 | 8,614,988,000 | 15% | ||
| imam-samudra | 0 | 3,420,749,215 | 79% | ||
| ripusun | 0 | 20,364,126,051 | 100% | ||
| atyourservice | 0 | 1,025,229,749 | 6.4% | ||
| fredhill | 0 | 10,684,637,812 | 100% | ||
| lion-bull | 0 | 4,449,016,101 | 100% | ||
| rivasvu | 0 | 0 | 100% | ||
| puertajohi | 0 | 0 | 100% | ||
| reineesmay | 0 | 792,653,345 | 5.6% | ||
| andreseloy581 | 0 | 86,117,272,198 | 100% | ||
| shadowedraven | 0 | 733,285,628 | 40% | ||
| resonator | 0 | 4,883,745,644,217 | 15% | ||
| xappreciator | 0 | -150,600,028 | -10% | ||
| xtheycallmedan | 0 | -516,570,359 | -60% | ||
| xranchorelaxo | 0 | -111,126,957 | -100% | ||
| eunice9200 | 0 | 983,943,530 | 25% | ||
| oniriusz | 0 | 17,356,172,288 | 100% | ||
| growandbow | 0 | 10,415,467,665 | 100% | ||
| revise.spk | 0 | 6,457,385,166 | 100% | ||
| hive.aid | 0 | 52,871,641,372 | 100% | ||
| lekcje | 0 | 606,213,453 | 100% | ||
| blockbunnyorg | 0 | 3,717,150,641 | 100% | ||
| stream4fun | 0 | 577,065,403 | 30% | ||
| jayrent | 0 | 5,150,075,888 | 100% |
BTW, I have had a problem with loading photos for several months. I do not know why. I drag and drop and nothing happens (conditions are met, 2:1 max 5MB 4096x2048).
| author | bezkresu |
|---|---|
| permlink | re-disregardfiat-20221028t1345664z |
| category | hive |
| json_metadata | {"tags":["hive","dlux","ipfs","dev","security","dapp","defi"],"app":"ecency/3.0.28-vision","format":"markdown+html"} |
| created | 2022-10-27 23:34:57 |
| last_update | 2022-10-27 23:34:57 |
| depth | 1 |
| children | 2 |
| last_payout | 2022-11-03 23:34:57 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.000 HBD |
| curator_payout_value | 0.000 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 165 |
| author_reputation | 46,757,822,662,314 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,839,744 |
| net_rshares | 0 |
the public services we were using decided to not continue, so we're switch over to SPK network for file storage... which means we gotta build all this out ourselves. Hoping to have uploads back online in a week or two.
| author | disregardfiat |
|---|---|
| permlink | re-bezkresu-rkfs08 |
| category | hive |
| json_metadata | {"tags":["hive"],"app":"peakd/2022.10.3"} |
| created | 2022-10-28 00:00:09 |
| last_update | 2022-10-28 00:00:09 |
| depth | 2 |
| children | 1 |
| last_payout | 2022-11-04 00:00:09 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.012 HBD |
| curator_payout_value | 0.012 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 219 |
| author_reputation | 348,256,954,150,586 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,840,351 |
| net_rshares | 41,764,415,771 |
| author_curate_reward | "" |
| voter | weight | wgt% | rshares | pct | time |
|---|---|---|---|---|---|
| theb0red1 | 0 | 32,127,322,977 | 10% | ||
| dustbunny | 0 | 9,637,092,794 | 2.44% |
Good luck!
| author | bezkresu |
|---|---|
| permlink | re-disregardfiat-20221029t2236770z |
| category | hive |
| json_metadata | {"tags":["hive"],"app":"ecency/3.0.34-mobile","format":"markdown+html"} |
| created | 2022-10-29 00:23:06 |
| last_update | 2022-10-29 00:23:06 |
| depth | 3 |
| children | 0 |
| last_payout | 2022-11-05 00:23:06 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.000 HBD |
| curator_payout_value | 0.000 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 10 |
| author_reputation | 46,757,822,662,314 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,870,067 |
| net_rshares | 0 |
Thanks for writing up on the workings of dlux. How is it determined which links become a part of the list of authorized subdomains? Each dapp would submit a request to the owner of dlux.io to be included in the authorized list? Can dapps use this technology and still be served from their own domain? Or do they have to served as subdomains of dlux.io?
| author | borislavzlatanov |
|---|---|
| permlink | re-disregardfiat-rll9sz |
| category | hive |
| json_metadata | {"tags":["hive"],"app":"peakd/2022.11.1"} |
| created | 2022-11-19 09:46:12 |
| last_update | 2022-11-19 09:46:12 |
| depth | 1 |
| children | 0 |
| last_payout | 2022-11-26 09:46:12 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.000 HBD |
| curator_payout_value | 0.000 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 355 |
| author_reputation | 23,569,043,849,875 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 118,451,731 |
| net_rshares | 0 |
Congratulations @disregardfiat! You received a personal badge! <table><tr><td>https://images.hive.blog/70x70/http://hivebuzz.me/badges/pud.png?202211011251</td><td>You powered-up at least 10 HIVE on Hive Power Up Day!<br>Wait until the end of Power Up Day to find out the size of your Power-Bee.<br>May the Hive Power be with you! </td></tr></table> <sub>_You can view your badges on [your board](https://hivebuzz.me/@disregardfiat) and compare yourself to others in the [Ranking](https://hivebuzz.me/ranking)_</sub> **Check out the last post from @hivebuzz:** <table><tr><td><a href="/hive-122221/@hivebuzz/pum-202211"><img src="https://images.hive.blog/64x128/https://i.imgur.com/M9RD8KS.png"></a></td><td><a href="/hive-122221/@hivebuzz/pum-202211">Be ready for the 11th edition of the Hive Power Up Month!</a></td></tr><tr><td><a href="/halloween/@hivebuzz/halloween-2022"><img src="https://images.hive.blog/64x128/https://i.imgur.com/jeLRU6l.png"></a></td><td><a href="/halloween/@hivebuzz/halloween-2022">Trick or Treat - Share your scariest story and win your Halloween badge</a></td></tr><tr><td><a href="/hive-122221/@hivebuzz/pud-202211"><img src="https://images.hive.blog/64x128/https://i.imgur.com/805FIIt.jpg"></a></td><td><a href="/hive-122221/@hivebuzz/pud-202211">Hive Power Up Day - November 1st 2022</a></td></tr></table>
| author | hivebuzz |
|---|---|
| permlink | notify-disregardfiat-20221101t132319 |
| category | hive |
| json_metadata | {"image":["http://hivebuzz.me/notify.t6.png"]} |
| created | 2022-11-01 13:23:18 |
| last_update | 2022-11-01 13:23:18 |
| depth | 1 |
| children | 0 |
| last_payout | 2022-11-08 13:23:18 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.000 HBD |
| curator_payout_value | 0.000 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 1,344 |
| author_reputation | 370,085,249,338,367 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,969,151 |
| net_rshares | 0 |
Great!! keep improving the app for everyone! i give you my witness vote to help you !
| author | malos10 |
|---|---|
| permlink | re-disregardfiat-20221027t133615552z |
| category | hive |
| json_metadata | {"tags":["hive","dlux","ipfs","dev","security","dapp","defi"],"app":"ecency/3.0.28-vision","format":"markdown+html"} |
| created | 2022-10-27 17:36:18 |
| last_update | 2022-10-27 17:36:18 |
| depth | 1 |
| children | 0 |
| last_payout | 2022-11-03 17:36:18 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.000 HBD |
| curator_payout_value | 0.000 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 87 |
| author_reputation | 677,191,552,355,945 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,832,285 |
| net_rshares | 0 |

| author | urun |
|---|---|
| permlink | re-disregardfiat-rki1xb |
| category | hive |
| json_metadata | {"tags":["hive"],"app":"peakd/2022.10.3"} |
| created | 2022-10-29 05:29:36 |
| last_update | 2022-10-29 05:29:36 |
| depth | 1 |
| children | 0 |
| last_payout | 2022-11-05 05:29:36 |
| cashout_time | 1969-12-31 23:59:59 |
| total_payout_value | 0.000 HBD |
| curator_payout_value | 0.000 HBD |
| pending_payout_value | 0.000 HBD |
| promoted | 0.000 HBD |
| body_length | 80 |
| author_reputation | 94,129,224,984,132 |
| root_title | "DLUX dApp Security Deep Dive" |
| beneficiaries | [] |
| max_accepted_payout | 1,000,000.000 HBD |
| percent_hbd | 10,000 |
| post_id | 117,874,395 |
| net_rshares | 0 |
 hiveblocks
hiveblocks